What Is Secure Processing?
Mission-critical systems at the core of aerospace and defense applications are subject to the same security vulnerabilities as advanced systems in other industries. However, the consequences of a security breach are far worse. Security must be built in, not bolted on as an afterthought. Technologies such as FPGA-based cryptography, root of security, secure boot, sensors, fingerprinting and physical protections against system infiltration are just some of the ways to protect mission-critical systems.
CHALLENGE
Protect the system.
Protect the mission.
SOLUTION
Advanced cryptography, secure boot and physical protection technologies like our BuiltSECURE™ technology can mitigate reverse engineering, deliver cyber resiliency and safeguard confidential data and IP against adversarial threats even when a system has been compromised. Combine BuiltSECURE™ technologies with our systems security engineering services to provide the ultimate in security.

System Security Engineering (SSE) for
End-to-End Protection
Mercury’s experienced system security engineers and customer support teams deliver affordable, end-to-end product security services including vulnerability assessments, technical training, and product-specific protection schemes.
Our SSE services include:
- Cybersecurity partner pre-integration
- Program protection planning assistance
- Red team/Blue team vulnerability analysis
A Comprehensive Security Portfolio
Our comprehensive physical security solutions, coupled with proven cybersecurity hardware technologies, offer world-class defense for high-value technology systems deployed in mission-critical applications.
Our security suite includes features such as basic access controls, write protection for NVM (or sanitization protocols) and protection for data, both at rest and at runtime. It also provides comprehensive key and crypto-engine management with built-in side channel attack (SCA) resistance, advanced sensing and fingerprinting capabilities, and industry-leading physical security. Together, these capabilities secure firmware management for updates and boot-time checks, and maintain system integrity.
THE MERCURY ADVANTAGE
BUILT-IN SECURITY
Confidently deploy mission-critical technology with physical and cybersecurity protection, built in, not bolted on.
ENHANCED RELIABILITY
Proven extended reliability and dependability through better cooling, component selection, environmental protection and testing.
COTS TECHNOLOGY
Reduce development time and expense with purpose-built products using commercial-off-the-shelf (COTS) technology.
SWAP OPTIMIZATION
Operate in the most challenging edge environments with size, weight and power (SWaP)-optimized solutions from chip-scale to system-scale.
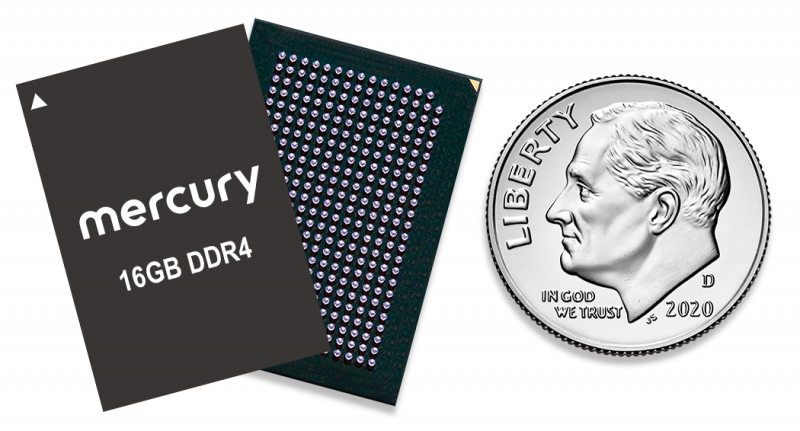
Trusted Microelectronics
Trusted Supply Chain Starting at Chip Scale
To deliver the latest commercial technology purpose-built for mission-critical aerospace and defense applications, we start at chip scale with our high-density system-in-package technology, designed and manufactured in trusted and secure DMEA-accredited facilities.
Trusted Supply Chain
Secure Products Delivered Uncompromised
BuiltSECURE products are designed and manufactured in trusted IPC-1791 certified and DMEA-accredited facilities to minimize the risk of back doors, counterfeits, and trojans.